What follows are selected quotations reprinted with permission from ETP, Engineering and Technology Publishing. This article was published in the International Journal of Renewable Energy and Smart Grid (IJRESG), (Vol. 1, No. 1), September 2012.
Smart Grid Security: Threats, Vulnerabilities and Solutions
Abstract for Article:
“The traditional electrical power grid is currently evolving into the smart grid. Smart grid integrates the traditional electrical power grid with information and communication technologies (ICT). Such integration empowers the electrical utilities providers and consumers, improves the efficiency and the availability of the power system while constantly monitoring, controlling and managing the demands of customers. A smart grid is a huge complex network composed of millions of devices and entities connected with each other. Such a massive network comes with many security concerns and vulnerabilities. In this paper, we survey the latest on smart grid security. We highlight the complexity of the smart grid network and discuss the vulnerabilities specific to this huge heterogeneous network. We discuss then the challenges that exist in securing the smart grid network and how the current security solutions applied for IT networks are not sufficient to secure smart grid networks. We conclude by over viewing the current and needed security solutions for the smart gird.”
Selected quotations from this article are as follows:
“[The] Smart grid network introduces enhancements and improved capabilities to the conventional power network making it more complex and vulnerable to different types of attacks. These vulnerabilities might allow attackers to access the network, break the confidentiality and integrity of the transmitted data, and make the service unavailable. … the following vulnerabilities are the most serious in smart grids:
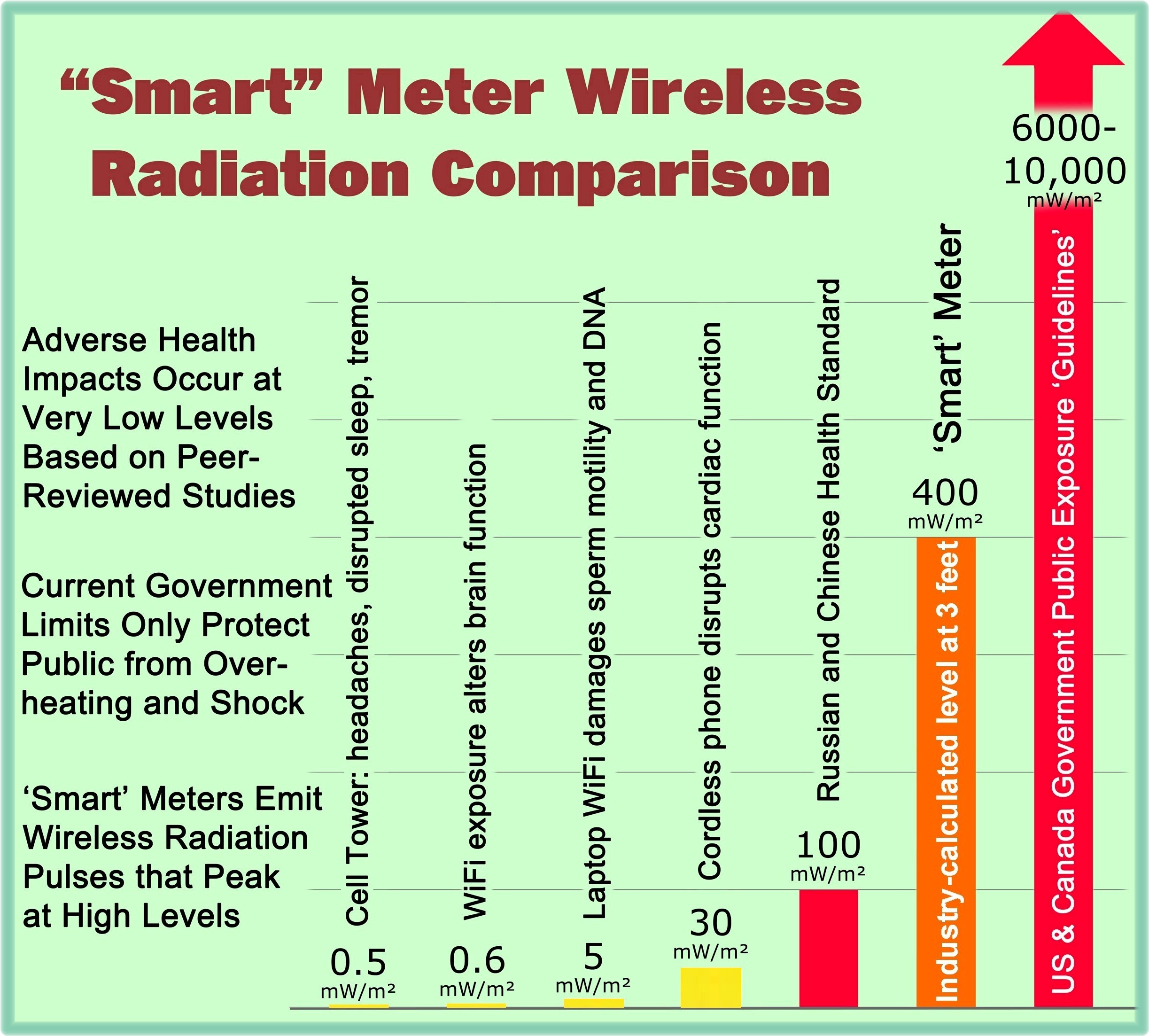
1) Customer security: Smart meters autonomously collect massive amounts of data and transport it to the utility company, consumer, and service providers. This data includes private consumer information that might be used to infer consumer’s activities, devices being used, and times when the home is vacant. [emphasis added]
2) Greater number of intelligent devices: A smart grid has several intelligent devices that are involved in managing both the electricity supply and network demand. These intelligent devices may act as attack entry points into the network. Moreover, the massiveness of the smart grid network (100 to 1000 times larger than the internet) makes network monitoring and management extremely difficult.
3) Physical security: Unlike the traditional power system, smart grid network includes many components and most of them are out of the utility’s premises. This fact increases the number of insecure physical locations and makes them vulnerable to physical access.
4) The lifetime of power systems: Since power systems coexist with the relatively short lived IT systems, it is inevitable that outdated equipments are still in service. This equipment might act as weak security points and might very well be incompatible with the current power system devices.
5) Implicit trust between traditional power devices: Device-to-device communication in control systems is vulnerable to data spoofing where the state of one device affects the actions of another. For instance, a device sending a false state makes other devices behave in an unwanted way.
6) Different Team’s backgrounds: Inefficient and unorganized communication between teams might cause a lot of bad decisions leading to much vulnerability.
7) Using Internet Protocol (IP) and commercial off-the- shelf hardware and software: Using IP standards in smart grids offer a big advantage as it provides compatibility between the various components. However, devices using IP are inherently vulnerable to many IP-based network attacks such as IP spoofing, Tear Drop, Denial of Service, and others.
8) More stakeholders: Having many stakeholders might give raise to a very dangerous kind of attack: insider attacks.”
“The just mentioned vulnerabilities can be exploited by attackers with different motives and expertise and could cause different levels of damage to the network. Attackers could be script kiddies, elite hackers, terrorists, employees, competitors, or customers. The authors in [4] group attackers into:
1) Non-malicious attackers who view the security and operation of the system as a puzzle to be cracked. Those attackers are normally driven by intellectual challenge and curiosity.
2) Consumers driven by vengeance and vindictiveness towards other consumers making them figure out ways to shut down their home’s power.
3) Terrorists who view the smart grid as an attractive target as it affects millions of people making the terrorists’ cause more visible.
4) Employees disgruntled on the utility/customers or ill-trained employees causing unintentional errors.
5) Competitors attacking each other for the sake of financial gain.”
“The massiveness of the smart grid and the increased communication capabilities make it more prone to cyber attacks. [emphasis added] Since the smart grid is considered a critical infrastructure, all vulnerabilities should be identified and sufficient solutions must be implemented to reduce the risks to an acceptable secure level.”
[4] Flick T and Morehouse J. Securing the Smart Grid: Next Generation Power Grid Security. Syngress, 2010.
[Above selected quotations reprinted with permission from ETP, Engineering and Technology Publishing. Articles were published in the International Journal of Renewable Energy and Smart Grid (IJRESG), (Vol. 1, No. 1), September 2012.]
The complete article may be viewed at the following link:
http://www.ijsgce.com/uploadfile/2012/1011/20121011121836539.pdf.